Monday starts with a familiar pattern. You open your laptop, check overnight tickets, and find a cluster of security alerts that all look urgent but none look clear.
One alert points to suspicious outbound traffic. Another flags a remote user’s device. Microsoft 365 shows an unusual sign-in attempt that might be harmless, or might not. While you are trying to work out what needs action first, users are already asking why VPN access is slow, whether a new cloud app can be approved, and why finance cannot reach a supplier portal.
For many IT managers in the East Midlands, that is the core problem. The firewall is not absent. It is there, powered on, licensed, and technically doing something. The issue is that a firewall without active management creates work instead of reducing risk.
That reactive loop wears teams down. It also leaves gaps. Rules get added but not reviewed. Firmware updates slip because there is never a good time. Logs exist, but nobody has time to examine them properly. Compliance questions arrive before the audit, not during normal operations. In Microsoft 365 and Azure estates, the problem gets worse because the old network edge no longer tells the whole security story.
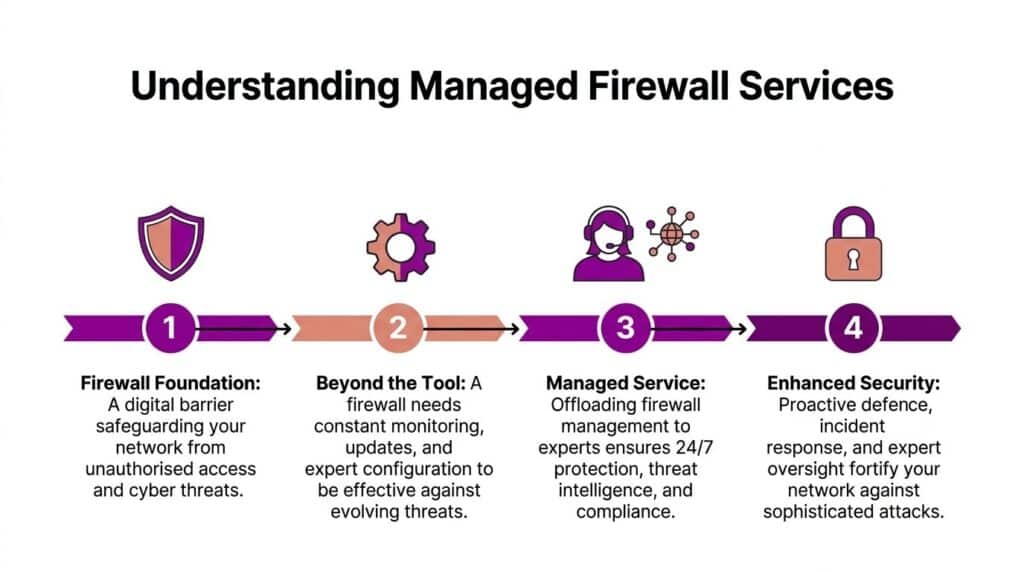
A managed firewall service changes that. It turns the firewall from a box you maintain into a security function that is monitored, tuned, reviewed, and aligned with how your business operates.
Beyond the Default Your Business’s Security Wake-Up Call
The most dangerous security setups are often the ones that look fine at a glance.
A mid-sized business might have a reputable firewall, Microsoft 365 Business Premium or E5, conditional access in place, and endpoint protection deployed. On paper, that sounds organised. In practice, many environments still rely on one internal person to handle alerts, rule changes, internet access policies, VPN issues, patch windows, and compliance evidence.
That person is usually not under-skilled. They are overloaded.
The result is predictable. Security becomes event-driven. A user reports something strange. A vendor requests access. A director asks whether the company is protected against ransomware. An auditor asks for logs and policy evidence. The firewall then becomes a source of last-minute work rather than an always-on control.
Where pressure shows up
Three pressure points appear again and again in growing businesses:
- Alert fatigue: Security notifications arrive faster than they can be triaged.
- Rule sprawl: Temporary access rules stay in place because nobody has time to review them properly.
- Cloud confusion: Traffic no longer sits neatly behind one perimeter once staff use Microsoft 365, Azure services, and remote devices.
A default firewall deployment does not solve those operational problems. It only creates the possibility of solving them.
A strong security posture depends less on owning the right hardware and more on whether someone is accountable for its daily operation.
That is why managed firewall services matter. They move ownership away from ad hoc administration and into a defined operational model. Someone monitors health. Someone checks rule changes. Someone reviews suspicious activity in context. Someone keeps the platform current.
For an IT manager, the gain is not only technical. It is mental space. You stop spending half the week deciding whether a firewall event deserves attention and start spending time on projects the business values.
What Is a Managed Firewall Service
A managed firewall service is the ongoing operation of your firewall by a specialist team rather than by your internal staff alone.
The firewall itself is the enforcement point. It controls what traffic is allowed, blocked, inspected, or prioritised between your users, devices, applications, sites, and the wider internet. The managed service is the operational layer around it. That is where the primary value sits.
The difference between owning and managing
Buying a firewall appliance or subscribing to a cloud firewall platform gives you capability. It does not give you continuous protection by itself.
A managed service usually covers work such as:
- Initial design: Building policies that reflect how your users, offices, remote workers, and cloud apps function.
- Rule administration: Adding, changing, and removing firewall rules without letting exceptions pile up.
- Monitoring: Watching for suspicious events, failed connections, policy violations, unusual traffic patterns, and service health issues.
- Patch and firmware management: Keeping the firewall current so known weaknesses are not left exposed.
- Incident response support: Investigating whether a security event is noise, misconfiguration, or a genuine threat.
- Reporting: Producing evidence that helps IT leaders, senior management, and auditors understand the current position.
That is why a managed firewall service is closer to hiring a security operations function than outsourcing a device.
What the managed part should include
Not every provider means the same thing by “managed”.
Some providers only offer basic administration. They will make rule changes on request and keep licensing current. That may be enough for a simple environment, but it is not what most growing organisations need.
A more mature service includes:
- Policy ownership so rules are reviewed against risk, not just implemented when requested.
- Operational visibility so somebody notices suspicious activity before users report symptoms.
- Escalation paths so incidents do not stall in a generic helpdesk queue.
- Alignment with wider security controls so the firewall works with endpoint, identity, and cloud protections.
If you are comparing providers, it helps to understand how broader managed network security solutions are typically positioned. The useful question is whether the provider treats the firewall as a standalone product or as one layer in a joined-up security model.
What a managed firewall service is not
It is not a substitute for every other security control.
It will not replace good Microsoft 365 identity security, endpoint detection, backup strategy, user awareness, or sensible access governance. It also will not fix a badly structured Azure environment on its own.
What it should do is give you disciplined control at the network and traffic layer, backed by people who know how to operate that layer properly.
Managed Firewall Versus In-House Management
The in-house versus outsourced decision is rarely ideological. It is operational.
Most IT managers know their environment better than any outside provider at the start. They know which line-of-business app needs an odd port opened, which warehouse site has flaky connectivity, and which supplier insists on legacy access methods. That local knowledge matters. The question is whether your internal team can turn that knowledge into consistent firewall operations every day.
What in-house gets right
Managing the firewall internally gives you direct control. Changes can be made quickly if the right person is available. Internal teams also understand business context without needing a handover.
That model works best when you already have security-focused staff, documented processes, and the time to review firewall policy as a living control rather than a static setup.
The problem is not technical ability. It is coverage.
If one person handles infrastructure, Microsoft 365 administration, support escalations, and supplier coordination, firewall management becomes one more responsibility competing for attention. In many businesses, that means monitoring is irregular, policy review is delayed, and out-of-hours issues become tomorrow’s problem.
What managed services usually improve
A managed firewall service gives you access to a team with a narrower focus. They spend more time looking at firewall behaviour, configuration quality, logging, patching, and incident patterns than a generalist internal team can.
That usually leads to better operational discipline in a few areas:
- Change control: Rule requests get reviewed against risk and necessity.
- Availability: Somebody is responsible outside your normal office hours.
- Platform hygiene: Firmware, subscriptions, and policy reviews are less likely to drift.
- Escalation: Security events have an owner, not just a ticket.
Comparison table
| Factor | In-House Management | Managed Firewall Service |
|---|---|---|
| Day-to-day ownership | Usually sits with one internal engineer or a small IT team | Sits with a specialist provider operating defined processes |
| Coverage | Depends on staff availability, leave, and competing priorities | Typically offers ongoing monitoring and structured response |
| Skills depth | Strong business context, but often broad rather than specialised | Broader exposure to firewall operations across multiple environments |
| Rule reviews | Can become reactive and request-driven | More likely to be handled as part of service governance |
| Patch management | May be delayed to avoid disruption or because time is limited | Usually scheduled and tracked as part of managed operations |
| Incident handling | Can be slowed by workload or lack of specialist capacity | Faster triage when the provider has clear escalation procedures |
| Scalability | Harder when new sites, users, or cloud workloads are added | Easier to extend if the service model is built for growth |
| Internal IT focus | Security admin competes with projects and support work | Internal staff regain time for business-facing initiatives |
The hidden cost issue
The headline comparison often starts in the wrong place. Teams compare a monthly managed service fee against the purchase and licence cost of a firewall. That misses the central issue.
The accurate comparison is between a service fee and the cost of internal time, specialist knowledge, monitoring discipline, policy maintenance, and security risk if those things are inconsistent. In smaller and mid-sized organisations, those hidden costs are often what push teams towards outsourcing.
If your firewall only gets proper attention after an incident, you are not really managing it. You are recovering around it.
A practical rule for deciding
Keep management in-house if you can answer yes to all of these:
- Do we have named security ownership for firewall operations?
- Can we monitor and respond outside standard working hours?
- Do we review rules, logs, and firmware as scheduled tasks rather than ad hoc jobs?
- Can we integrate firewall decisions with Microsoft 365, endpoint, and Azure security?
If the answer is no to even one or two, a managed firewall service usually becomes the more reliable option.
Not because internal teams are weak. Because most SMB IT teams have too much to carry already.
Key Capabilities of a Modern Managed Firewall
A modern managed firewall is not just a port filter with a support contract. It should function as one part of a wider security control set.
The important point is how the pieces work together. Strong services do not merely enable features. They tune them around business use, review what they are seeing, and adjust policy as your environment changes.
Core controls that still matter
At the base level, a managed firewall should provide disciplined handling of traffic between users, devices, locations, and applications.
That usually includes:
- Stateful inspection and rule enforcement to allow or block traffic according to policy.
- Network segmentation support so critical systems are not exposed to the same access profile as general office users.
- Secure remote access controls where legacy VPN still exists and needs careful management.
- Logging and audit trails so you can investigate events and support compliance work.
These are not glamorous features, but they are the controls that stop the environment becoming chaotic.
Next-generation features that earn their place
The stronger services add next-generation firewall capabilities that help with current attack methods and user behaviour.
A mature stack often includes:
- Intrusion prevention that blocks known malicious activity, not just records it.
- Application control so access can be based on the actual application, not only destination and port.
- Web filtering to reduce exposure to harmful or inappropriate destinations.
- Threat intelligence integration so policy and detection can react to emerging indicators.
- Encrypted traffic inspection options where risk and privacy requirements allow it.
Used well, these controls reduce both noise and exposure. Used badly, they create disruption, false positives, and user resentment. Management quality matters as much as feature lists.
Visibility is a capability, not a nice-to-have
One of the biggest differences between average and effective services is reporting.
Useful reporting shows what is being blocked, what is being allowed, where unusual traffic appears, which rules are being used, and where policy drift is creeping in. It also presents that information in a way that an IT manager can use for decisions, not just archive for later.
If you want a sense of how these capabilities fit into a wider defensive approach, this overview of network security and firewall services is useful: https://www.f1group.com/network-security-and-firewalls/
The best firewall service does not produce the most alerts. It produces the clearest decisions.
Why integration matters more than feature count
A long feature list can look impressive in a proposal. It means little if those features sit in isolation.
A modern managed firewall should feed into endpoint security, identity controls, remote access design, and cloud policy. If your firewall spots suspicious outbound behaviour but nobody checks whether the user’s Microsoft sign-in activity looks odd at the same time, the investigation remains incomplete.
That is why capability should be judged by operational fit, not marketing language. Features matter. Coordination matters more.
The Business Case Security Compliance and Cost Savings
The strongest argument for a managed firewall service is not that it is fashionable or technically advanced. It is that it reduces business exposure while making security operations easier to justify and govern.
For organisations that have grown beyond a very small internal setup, firewall management stops being a minor admin task. It becomes part of risk management, audit readiness, and service continuity.
Security value that boards understand
Boards and leadership teams do not need a lesson in ports, protocols, or inspection engines. They need to understand what happens when controls are weak.
A managed firewall service helps in practical terms:
- Reduced operational disruption: Suspicious traffic and poor rule hygiene are less likely to become business outages.
- Clearer accountability: There is a named service with defined ownership instead of diffuse responsibility.
- Better response discipline: Events are triaged and escalated through a process rather than informal judgement.
Security failures are rarely tidy; they interrupt operations, absorb staff time, and create reputational stress long before any formal recovery work starts.
Compliance becomes easier to evidence
For many SMBs, the pain point is not only security. It is proving that security controls are being managed consistently.
Managed services can make that easier through regular reporting, change tracking, logging, and policy review. That is useful for GDPR discussions, PCI DSS-related controls, cyber insurance questions, and internal governance checks.
The gain is not that compliance becomes automatic. It does not. The key advantage is that evidence is easier to gather because routine operational data is already being captured and reviewed.
A managed service is especially relevant when the firewall also supports cloud connectivity and Azure resources. That is where network policy and cloud security responsibilities can overlap. Organisations that want a more joined-up Microsoft cloud approach often look at related Azure support models such as https://www.f1group.com/managed-azure-services/
The ROI question
Here, many generic articles become vague. They talk about protection but avoid the financial discussion management teams seek.
For UK SMBs with 50-500 employees, the financial justification for a managed firewall is critical. While many services highlight compliance, the primary ROI comes from quantifiable cost savings. A detailed cost-benefit analysis often reveals significant savings from reduced in-house staffing needs, avoidance of breach costs (which can be crippling for SMBs), and increased efficiency during compliance audits, far outweighing the monthly service fee (Hughes).
That reflects what many IT leaders already suspect. The visible monthly fee is only one part of the picture. Internal effort, delayed projects, out-of-hours firefighting, and audit preparation all carry cost even when they do not show up neatly under one budget line.
A short explainer can help frame that conversation internally.
Where cost savings usually appear
The most credible savings often come from three places:
- Specialist staffing pressure drops because the business does not need to build every firewall skill internally.
- Incident impact is contained earlier when monitoring and operational ownership are stronger.
- Compliance preparation takes less effort because logs, rule history, and change records are already available.
That does not mean every managed firewall service is automatically good value. Poorly scoped services can still produce overlap, slow change handling, or weak reporting. But when the service is designed properly, the business case is usually stronger than many organisations expect.
How to Choose the Right Managed Firewall Partner
Choosing a partner is less about brand logos and more about operational fit. The right provider should be able to explain how they will run your firewall estate day to day, how they will work with your Microsoft environment, and what happens when something goes wrong.
A lot of organisations start with the wrong question. They ask which firewall vendor the provider supports. That matters, but it is not the first issue. The first issue is whether the provider can operate security as a service, not just administer a device.
If you want a plain-English refresher on what a Managed Service Provider (MSP) does in general, that background can be useful before you compare specialist security capability.
Start with service ownership
Ask who owns what once the contract starts.
You need clear answers on:
- Monitoring responsibility: Who watches the platform and associated alerts?
- Change process: How are rule changes requested, reviewed, approved, and documented?
- Escalation: What happens if the provider sees suspicious activity at night or over a weekend?
- Service boundaries: Which tasks are included, and which are billable extras?
Weak providers stay high level here. Strong ones describe workflow, accountability, and communication.
Check the Microsoft 365 and Azure story
Many firewall conversations become outdated here.
For organisations migrating to Microsoft 365 and Azure, a critical question is how a traditional managed firewall interacts with cloud-native security like Microsoft Defender and Azure Firewall. A competent provider must offer a clear strategy for integrating these tools to avoid security gaps or redundant costs, addressing how their service supports modern security models like Zero Trust Network Access (ZTNA) and specific UK data residency requirements (SonicWall).
That is the right test. If a provider only talks about perimeter protection and site-to-site connectivity, they are behind the current state of modern estates.
Ask direct questions such as:
- How do you align firewall policy with Microsoft Defender signals?
- When would you recommend Azure Firewall versus an on-premises or edge firewall?
- How do you handle remote access if we want to reduce reliance on legacy VPN?
- How do you avoid duplicated spend across firewall, endpoint, and cloud controls?
- What is your approach to UK data residency concerns in Microsoft-based environments?
A capable provider should be comfortable discussing conditional access, identity-led controls, cloud segmentation, and traffic visibility across hybrid estates.
Review SLAs like an operator, not a buyer
Service Level Agreements are often skimmed. That is a mistake.
Look for specifics around:
- Response times: Not just for critical incidents, but for normal change requests.
- Escalation paths: Named routes for technical, service, and security issues.
- Maintenance handling: How firmware and policy updates are scheduled and communicated.
- Reporting cadence: How often you receive operational and governance reporting.
The right SLA reflects how your business runs. A manufacturing site, charity, legal practice, and multi-branch retailer do not all carry the same operational risk.
A managed firewall service is only as good as the provider’s behaviour at 17:30 on a Friday when an access issue lands and your own team is already stretched.
Ask for governance, not just support
Day-to-day support matters, but governance is what keeps the service useful over time.
You want regular review of:
- Rule base quality
- Unused or risky exceptions
- Emerging traffic patterns
- Cloud application changes
- Remote access design
- Compliance evidence needs
If the provider does not review these things with you, the service can slowly become a ticket-taking function.
A stronger option is a provider that can also support wider managed security services where the firewall is one layer among several. This broader context matters more in Microsoft-centric environments: https://www.f1group.com/it-managed-security-services/
Favour practical sector experience
The ideal partner has worked with businesses of your size and complexity, not only with large enterprises or very small firms.
Ask about experience with environments like yours:
- Hybrid Microsoft 365 and on-premises setups
- Multiple sites across the East Midlands
- Remote and office-based workers
- Sector-specific compliance pressures
- Legacy line-of-business applications that still need controlled access
A provider who has seen these patterns before is more likely to design sensible policy from the start.
Local presence still matters
Even with strong remote tools, local or regional presence has practical value.
When there is a site issue, an office move, a connectivity cutover, or a live incident that needs on-site coordination, being close enough to respond matters. It also helps when governance meetings need to involve IT, operations, and leadership in the same room.
This is especially relevant for East Midlands organisations where branch offices, warehouses, and mixed connectivity environments are common. A local provider usually understands those realities better than a remote-only team operating from a national queue.
A shortlist test that works
Before signing, give each shortlisted provider a realistic scenario.
For example:
- A user in finance needs urgent access to a new third-party portal.
- A warehouse loses connectivity to a cloud application.
- Microsoft flags risky sign-in behaviour on an account that also generated unusual outbound traffic.
- An auditor asks for evidence of recent firewall rule changes and approvals.
Then ask the provider to explain their response process. Not in marketing terms. In steps.
The provider worth trusting is the one whose answer sounds calm, structured, and operationally credible.
Secure Your Network and Empower Your Business Today
Security gets harder when the business grows faster than the controls around it. More users, more remote access, more Microsoft 365 services, more cloud workloads, and more audit pressure all place extra strain on the same internal team.
A managed firewall service gives that team room to breathe.
It replaces fragmented firewall administration with defined ownership, monitoring, policy discipline, and clearer integration with the rest of your security stack. That does not remove the need for internal IT leadership. It strengthens it. Your team can focus on change, user experience, Microsoft roadmap decisions, and business projects instead of constantly reacting to the next alert.
For East Midlands organisations, the best results usually come when firewall management is treated as part of a wider Microsoft-led security model. The firewall still matters. It just needs to fit properly alongside Microsoft 365 identity controls, endpoint protection, Azure services, and practical compliance requirements in the UK.
If your current setup depends on one busy internal person keeping everything together, the risk is not only technical. It is operational. It is the slow drift that happens when security work is always important but rarely urgent until something breaks.
That is the point where a managed service becomes worth serious consideration.
A good partner will help you reduce noise, tighten policy, support compliance, and make better decisions about where firewall controls end and cloud-native security should take over. That is what turns the firewall from a maintenance burden into a useful part of your business defence.
Take the next step. Phone 0845 855 0000 today or Send us a message at https://www.f1group.com/contact/ to schedule a no-obligation consultation.
F1Group helps organisations across the East Midlands secure and support Microsoft-focused IT environments with practical, hands-on expertise. If you want a clearer, more reliable approach to firewall management, Microsoft 365 security, and Azure-aligned protection, Phone 0845 855 0000 today or Send us a message https://www.f1group.com/contact/.

