In the UK, it’s best to think of penetration testing as a non-negotiable security MOT for your business. It’s a controlled, ethical simulation of a real-world cyberattack. The whole point is to find the cracks in your digital defences before a criminal does, saving you from what could be devastating financial and reputational fallout.
Why Your Business Needs a Security MOT
You wouldn’t run a fleet of delivery vans without getting them through their annual MOT, would you? The same logic applies to your company's digital presence. For UK businesses, especially small and medium-sized organisations in places like the East Midlands that are embracing new technology, this isn't some high-tech luxury. It's a core part of managing business risk.

Before we get into the nuts and bolts of testing, it’s worth taking a step back. A penetration test is one of the most powerful tools in your security toolkit, but it's part of a bigger picture. Getting a handle on understanding network security and its importance provides the context for why these tests are so critical.
To give you a clearer picture, here’s a quick summary of what penetration testing means for a UK business.
Quick Look at Penetration Testing in the UK
| Aspect | Key Takeaway for UK Businesses |
|---|---|
| Core Concept | An authorised, simulated cyberattack to identify and fix security vulnerabilities. |
| Key Benefit | Proactively secures systems, preventing data breaches and operational downtime. |
| Business Case | Protects against financial loss, reputational damage, and regulatory fines. |
| UK Compliance | Essential for meeting standards like GDPR, PCI DSS, and Cyber Essentials. |
| Target | Not just for big corporations; crucial for SMEs who are increasingly targeted. |
This table neatly summarises the essentials, but it's the real-world context that truly brings home the urgency.
The Rising Tide of Cyber Threats in the UK
Cybercrime isn’t just a headline about a multinational bank. It’s a genuine, everyday threat to businesses of all sizes right here in the UK. Attackers are getting smarter, and they often see SMEs as softer targets precisely because their defences might not be as robust.
A single successful breach can trigger a cascade of problems:
- Significant financial loss: Think beyond the initial theft. You have to factor in the cost of fixing the damage, potential regulatory fines, and lost income while your systems are down.
- Irreversible reputational damage: When you lose customer data, you lose trust. Rebuilding that trust can take years, if it’s even possible.
- Legal and compliance penalties: A breach involving personal data can lead to serious fines under regulations like GDPR.
These aren't hypotheticals. Cyber incidents cost UK businesses an estimated £27.3 billion annually. In response, organisations are finally taking decisive action. An incredible 92% of UK organisations increased their cybersecurity budgets last year, with 85% of those specifically funnelling more investment into penetration testing to harden their defences.
More Than Just Finding Flaws
A proper, professional penetration test does so much more than just hand you a list of problems. It gives you a strategic roadmap to genuinely improve your security.
You’ll get a clear, prioritised action plan based on real-world risk, so you can put your time and money where it will make the biggest difference. It transforms security from a reactive expense into a smart, proactive investment in your company’s future and resilience.
Ready to secure your business? The first step is a simple conversation. Phone 0845 855 0000 today or Send us a message to discuss how a penetration test can protect your organisation.
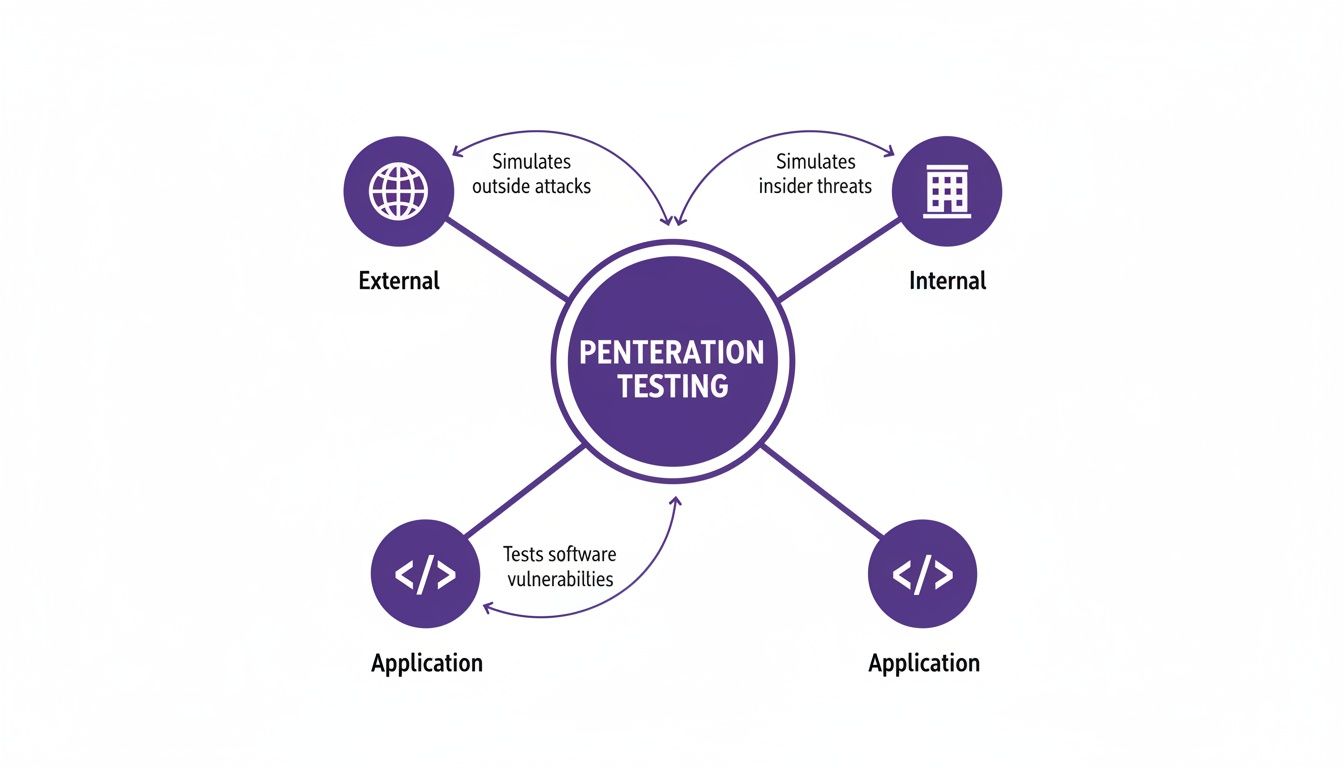
What Are the Different Kinds of Penetration Test?
Deciding you need a penetration test is a great first move, but it's crucial to understand that not all tests are created equal. Think of it like this: you wouldn't use the same insurance policy for your office building as you would for your company vehicles. In the same way, your digital assets—from your public-facing website to your internal servers—each need a specific type of security test to find the vulnerabilities that matter most.
Getting the right type of penetration testing in the UK means you’re not just ticking a box; you’re strategically checking your defences from the angles an attacker would actually use.
External Network Penetration Testing
This is probably what most people picture when they think of hacking. An external penetration test mimics an attack from a complete outsider on the internet who has zero inside information. Their goal is simple: to see if they can breach your outer walls and find a way into your organisation.
Our testers will essentially put on their black hats and start probing your publicly visible systems, looking for any crack in the armour. They’ll scrutinise things like:
- Your company website: Could it be defaced, or worse, could customer data be siphoned out?
- Email servers: Are there weaknesses that open the door to phishing attacks or business email compromise?
- Firewalls and routers: Can these perimeter guards be tricked or bypassed to get a foothold on the internal network?
- Other internet-facing services: This includes everything from the VPN your team uses for remote access to any other services you've exposed to the web.
This test answers the one question every business owner should be asking: "What could a determined attacker on the other side of the world do to us?"
Internal Network Penetration Testing
While we often focus on threats from the outside, the reality is that many of the most damaging security breaches start from within. An internal penetration test simulates what could happen if someone already has access to your local network. This could be a disgruntled employee, a contractor with too many permissions, or a hacker who has already bypassed your perimeter defences by stealing a user's password.
With this test, we assume the attacker is already inside the castle walls. The focus shifts to damage control. How far can they get? What sensitive data can they access? This is vital, because an internal threat can often go unnoticed for months, quietly causing chaos.
From a standard user’s starting point, our testers will attempt to escalate their privileges, aiming to become a full-blown administrator. They'll hunt for sensitive file shares, try to access confidential databases, and see if they can take control of the systems that run your business. For any organisation handling sensitive customer or financial information, understanding your internal resilience is just as important as securing your perimeter.
Web Application and Mobile App Testing
For many businesses, your website or mobile app isn't just a marketing tool—it's the primary way you interact with your customers. A security flaw here can be devastating, damaging your reputation and putting you in breach of regulations like GDPR. That's why we offer specialised tests that focus solely on these applications, going far deeper than a standard external test ever could.
We dig into the very fabric of the application, analysing everything from the login process and payment gateways to how it stores and handles user data. The goal is to find common but critical flaws like SQL injection or cross-site scripting (XSS), which could allow an attacker to steal your entire customer database or hijack user accounts. If your business runs an e-commerce site, a customer portal, or a mobile app, this type of penetration testing is absolutely non-negotiable.
Demand in this area is growing fast. The UK penetration testing market is projected for steady growth right through to 2031, largely fuelled by GDPR compliance pressures and the relentless increase in cyber attacks. We're seeing more and more businesses in finance, healthcare, and tech asking for web app tests and social engineering simulations, especially to secure their cloud services like Microsoft Azure and Microsoft 365. You can read more about this trend in recent market analysis about the UK's security sector growth.
Cloud Security Penetration Testing
Moving to the cloud with platforms like Microsoft Azure, AWS, or Google Cloud has brought huge benefits to UK businesses, but it has also opened up a whole new attack surface. A cloud penetration test isn't about testing the security of Amazon's or Microsoft's infrastructure—that's their job. It’s about checking if your configuration of their services is secure.
It’s surprisingly easy to make a simple mistake in your cloud setup that accidentally exposes huge volumes of sensitive data to the public internet. This test validates that your cloud environment is properly locked down, ensuring you haven't left a digital side door wide open.
Ready to find the right test for your business? Phone 0845 855 0000 today or Send us a message to discuss your specific security needs.
Navigating UK Compliance and Certification Standards
In the UK, getting a penetration test isn't just a box-ticking exercise. It's a fundamental part of your legal and regulatory duties, especially if you handle personal or financial data. A professional pentest report is more than just a list of technical findings; it's solid proof that you're taking your security responsibilities seriously.
But here’s the crucial bit: without the right permissions, a pentest is legally the same as a real cyber-attack. To stay on the right side of the law and get a truly valuable test, you need to understand the rules of the game and what separates a great penetration testing UK provider from a risky one.
The Legal Foundations of Ethical Hacking in the UK
The cornerstone of all ethical hacking in Britain is the Computer Misuse Act 1990. This piece of legislation makes it a criminal offence to access computer systems without permission, no matter what your intentions are. This means a penetration tester absolutely must have explicit, written authority from you before they touch a single thing.
This isn't a simple nod of approval. The agreement needs to be a detailed document that spells everything out:
- Scope: Exactly which systems, networks, and applications are in play.
- Timing: The specific dates and times when the test is allowed to happen.
- Limitations: Any sensitive areas or disruptive techniques that are completely off-limits.
Getting this wrong can land the testers in serious legal trouble and create a massive liability for your business.
Proving Your Commitment to Data Protection
Beyond the Computer Misuse Act, two major regulations are driving the need for penetration testing: GDPR and PCI DSS. A well-documented test is one of the most powerful ways to show you're compliant.
A penetration test report acts as vital evidence that you're proactively finding and fixing security weaknesses. If a breach ever does happen, this document can show regulators, customers, and insurers that you've been diligent in your duties.
The Data Protection Act 2018 and UK GDPR require organisations to have "appropriate technical and organisational measures" to protect data. Penetration testing is a perfect example of a 'technical measure' that proves your security controls actually work. Likewise, the Payment Card Industry Data Security Standard (PCI DSS) has an explicit requirement for regular penetration testing if you handle any payment card data.
The different types of tests help you meet these varied compliance needs.
As you can see, each test focuses on a different potential attack path. This allows you to tailor your testing to match specific compliance goals, whether that’s for GDPR, PCI DSS, or your own internal standards.
Finding a Trusted UK Provider with CREST and CHECK
With so much at stake legally, how do you find a provider you can trust? Thankfully, the UK has well-established industry accreditations that act as a quality stamp.
-
CREST (Council of Registered Ethical Security Testers): This is the go-to accreditation in the technical security world. A CREST-certified company has had its methods, business processes, and the skills of its testers thoroughly checked. Choosing a CREST firm gives you real peace of mind.
-
CHECK: This scheme is run by the National Cyber Security Centre (NCSC) and is designed for testing government systems and critical national infrastructure. While most SMEs won't need a full CHECK test, if a provider is part of the scheme, it signals an exceptionally high level of expertise and trustworthiness.
Working with a firm that holds these credentials ensures they know the law inside and out and are committed to doing things properly. To see how this fits into a broader security plan, it's worth reviewing the NCSC Cyber Assessment Framework. These certifications aren't just logos; they're your assurance that you're placing your trust in a capable and ethical partner.
Ready to turn compliance into a competitive advantage? Phone 0845 855 0000 today or Send us a message to discuss your specific security and compliance needs.
The Pentesting Process and What to Budget
So, what actually happens during a penetration test? It's easy to imagine a chaotic free-for-all, but the reality is a carefully managed project. Let's walk through the journey from that first conversation to the final report, so you can see exactly what's involved.
Along the way, we'll tackle the question on every business leader's mind: "How much is this going to cost?"
What to Expect: The 5 Stages of a Pen Test
A professional test follows a clear, methodical path. This structure is designed to find real-world risks without causing any disruption to your day-to-day operations.
Here's a step-by-step look at how it all unfolds:
-
Scoping & Planning: This is without a doubt the most critical phase. We’ll sit down with you to agree on the "rules of engagement" – defining precisely what we’re testing, what’s off-limits, and what your goals are. This initial groundwork ensures the test is safe, legal, and focused on what matters most to your business.
-
Reconnaissance: The ethical hacker starts by gathering information, just like a real attacker would. They’ll probe your systems from the outside to see what they can discover, mapping out your digital footprint and looking for any publicly available information that could give them an advantage.
-
Vulnerability Analysis & Exploitation: Now for the "ethical hacking" part. Using a mix of automated scanners and their own manual expertise, the testers will try to find and exploit weaknesses. The goal isn't to cause damage but to prove a vulnerability exists and demonstrate what a real attacker could do with it.
-
Reporting: Once the testing is done, you'll receive a comprehensive report. This is much more than a technical data dump. It's a business-focused document that clearly explains each finding, ranks them by risk, and gives you a practical, prioritised list of recommendations for fixing them.
-
Remediation & Re-testing: The report becomes your action plan. After your team has put the recommended fixes in place, the testers will often come back to perform a re-test. This crucial step verifies that the holes have been properly plugged, confirming your investment has genuinely improved your security.
What Drives the Cost of Penetration Testing in the UK?
There's no single price for penetration testing in the UK. The cost is tied directly to the time and skill needed to do the job properly. Think of it like getting building work done: fixing a garden gate is a very different job, with a very different price tag, to building a two-storey extension.
The final quote will come down to a few key things:
- Scope and Complexity: The bigger and more complicated your systems are, the longer it takes to test them. A simple website is one thing; a sprawling network with custom applications, cloud services, and dozens of servers is another entirely.
- Type of Test: An internal test, where the tester is looking for risks from inside your network, is often more involved than a standard external test. A deep-dive web application test can be even more labour-intensive.
- Tester Experience and Certification: You're paying for expertise. Using a CREST-accredited firm with seasoned testers costs more per day, but it’s an investment in quality. A typical day rate for a qualified, experienced UK penetration tester is around £1,000 – £1,500.
A word of warning: if you get a quote that seems too good to be true, it probably is. A price that works out to less than £500 a day is a massive red flag. It usually means you’re just getting a cheap automated scan, not a real, human-led penetration test that requires an expert's critical thinking.
Estimated Penetration Testing Costs in the UK (GBP)
To give you a better idea for budgeting, we've put together some typical price ranges for SMEs and mid-sized organisations in the UK. Remember, these are just estimates; a final quote will always depend on a detailed scoping call to understand your specific needs.
| Type of Test | Estimated Cost Range (GBP) | Typical for |
|---|---|---|
| Basic External Test | £2,500 – £5,000+ | SMEs wanting to check their internet-facing systems for obvious holes. |
| Internal Network Test | £4,000 – £10,000+ | Businesses looking to understand insider threats or test their post-breach resilience. |
| Web Application Test | £5,000 – £15,000+ | Companies with critical e-commerce sites, customer portals, or SaaS products. |
These figures show that a proper test is an investment. It’s about managing risk, not just ticking a box. If you’re looking to get a handle on all your systems, you may find our guide on how to conduct a comprehensive computer security audit useful.
Ready to get a clear picture of your security risks and costs? Give us a call on 0845 855 0000 or send us a message for a no-obligation chat about what you need.
How to Choose the Right Penetration Testing Partner
Picking a company to carry out a penetration test is one of the most important security decisions you'll make. This isn't just another supplier relationship; you're handing over the keys to your kingdom and trusting them to find the weak spots without breaking anything. The aim isn't just a one-off report but finding a genuine partner who becomes an extension of your team.
When you’re weighing up a penetration testing UK provider, you need to look well beyond the price. It’s all about asking the right questions to understand their expertise, their ethics, and how they actually work. This is the only way to ensure you get a thorough, valuable assessment rather than a cheap scan that ticks a box but leaves you exposed.
The Essential Vetting Checklist
When you’re on the phone with potential providers, you need a way to cut through the sales pitch. Think of it as an interview for a highly sensitive role. These questions will help you get to the heart of what they truly offer.
- Are your testers CREST certified? In the UK, CREST is the benchmark for quality. It’s an independent verification that the company’s methods and its testers’ skills are up to a very high standard.
- Can we see a sample report? This is your window into their world. Is the report clear? Does it explain risks in business terms? Crucially, does it give you specific, actionable steps to fix things, or is it just a raw data dump from a scanning tool?
- What does your post-test support look like? A great partner doesn’t just email a report and disappear. Ask if they schedule a follow-up call to walk you through the findings and if they'll be available to help your team during the remediation phase.
- What is your methodology? Get them to explain their process. A good answer will focus on a manual, human-led approach that goes far beyond simply running automated software.
- What experience do you have in our sector? If you work in finance, manufacturing, or healthcare, a partner who already knows the specific regulatory and operational pressures you face is worth their weight in gold.
This simple checklist gives you a solid framework for comparing providers and weeding out the ones that aren’t a good fit.
Accreditations and Experience Matter
Choosing your security partner based on the lowest quote is a classic false economy. A cheap test that misses one critical vulnerability can end up costing you infinitely more down the line. A provider's qualifications are your best signal of quality and reliability.
A provider’s certifications, like CREST, aren’t just logos for their website. They are your assurance that you are working with a professional, ethical, and technically competent organisation that understands the legal framework of ethical hacking in the UK.
Beyond the badges, look for real-world experience. Ask for case studies or references from businesses of a similar size and in a similar industry to your own. A company with a proven track record shows they can deliver results and build trust. It’s also a good time to see how their testing fits into a wider security strategy, like the ongoing protection offered by IT managed security services, to build a more robust defence.
The Advantage of a Regional Partner
While big national firms have their place, there’s a lot to be said for working with a regional provider, especially for businesses in areas like the East Midlands. A local partner often has a much better feel for the regional business community and can offer a more personal and flexible service.
That proximity helps build a much stronger, long-term relationship. It's simply easier to build a genuine rapport when your security partner is just down the road. They start to feel less like a contractor and more like a part of your own team, leading to more tailored advice and a partnership built on shared success. You're looking for someone invested in your security for the long haul, not just for a single project.
Building Your Long-Term Security Strategy
Getting your penetration test report back isn't the finish line. Far from it. Think of it as the first page of your new playbook for building a genuinely secure business. It’s this shift in mindset—viewing security as an ongoing cycle of improvement, not a one-off task—that truly separates well-protected organisations from the vulnerable ones.
This proactive stance is just good business sense in the modern UK economy. If your organisation relies on powerful platforms like Microsoft Azure or Dynamics 365, you already know that continuous investment is part of getting the most out of them. Security is no different. It’s your chance to stop reacting to problems and start confidently defending against them.
From Report to Resilience
So what does "moving forward" actually look like? It's about taking the findings from your report and weaving them into the fabric of your organisation. This means more than just patching the specific vulnerabilities that were found; it means establishing a rhythm of regular testing, monitoring, and training.
This is how you build genuine cyber resilience—the ability to withstand and recover from an attack.
A penetration test provides a high-resolution snapshot of your security at one moment in time. A strong long-term strategy turns that snapshot into a live video feed, showing you how your security landscape is evolving and helping you stay ahead of new threats.
Ultimately, penetration testing is a critical piece of a much larger puzzle: your overall Cybersecurity and data protection framework. It’s about safeguarding your customers, protecting your hard-earned reputation, and securing your company's future.
Your Next Steps to a Secure Future
This guide was designed to give you a clear, practical understanding of penetration testing in the UK. You now have the context you need to make smart, informed decisions to protect your business. The only thing left to do is act.
Take the first step in securing your organisation's future.
Phone 0845 855 0000 today or Send us a message to discuss your specific security needs.
Frequently Asked Questions About Penetration Testing
Even with a good grasp of the basics, there are always a few practical questions that crop up when a business is on the verge of its first pen test. It’s completely normal. We’ve had these conversations with countless IT managers and business owners, so let's clear up some of the most common ones.
Getting these details straight helps take the mystery out of the process and makes sure everyone, from the technical team to the board, is comfortable and on the same page.
Let's start with the big one we hear all the time: "Will this disrupt our business?" It’s a perfectly reasonable fear. The very idea of letting someone try to 'break' your systems sounds risky. In reality, a professional, ethical test is anything but chaotic.
It's all about control. The entire process is carefully managed to have a near-zero impact on your day-to-day operations. This is precisely what the scoping phase is for; we work closely with you to set clear 'rules of engagement'. That means scheduling tests for quiet periods—overnight or on a weekend—and agreeing which critical systems are off-limits or need to be handled with extreme care. Our goal is to find vulnerabilities, not to create them.
How Often Should We Be Doing This?
There’s no magic number for how often you should run a penetration test. The right schedule really comes down to your company's specific circumstances—it's a blend of your risk appetite, any compliance rules you fall under, and how quickly your technology changes.
As a general rule of thumb, testing at least once a year is a solid baseline.
However, you should definitely test more frequently if you’re:
- Making big changes: Rolling out a new web app, shifting services to a cloud platform like Azure, or making significant updates to your network architecture are all prime times for a test.
- Meeting compliance demands: Some regulations are very specific. PCI DSS, for example, explicitly requires a test at least annually and after any major system change.
- In a high-risk sector: If your business is in finance, healthcare, or you simply handle a lot of sensitive personal data, more frequent testing is just part of doing your due diligence.
Think of it less as a one-off MOT and more as a continuous health check for your digital footprint. It ensures your security keeps pace with your business.
The key takeaway is this: penetration testing should be seen as a continuous part of your security lifecycle, not a one-time event. It’s an ongoing health check for your digital assets.
Isn't This Just a Vulnerability Scan?
This is another point that often causes confusion. It’s easy to mix up an automated vulnerability scan with a manual, human-driven penetration test. They sound similar, but they are worlds apart in what they deliver. Mistaking one for the other can leave your business wide open.
Here’s the simple difference:
-
Vulnerability Scan: Think of this as an automated checklist. A piece of software scans your systems for thousands of known, pre-catalogued vulnerabilities. It’s fast and relatively cheap, but it has no intelligence or context. A scan can tell you a door is unlocked, but it can’t tell you what a thief could do once they get inside.
-
Penetration Test: This is a mission-driven exercise led by a creative human expert. A pen tester might use automated scans as a starting point, but that's where the similarities end. They then use their experience to think like a real attacker, chaining together seemingly minor flaws, escalating their privileges, and demonstrating a genuine business impact.
An automated scan will flag that you're using slightly outdated software. A human pen tester will figure out how to exploit that software to gain access and steal your customer database. That’s the real-world difference, and it’s why a proper penetration test provides a level of assurance that a simple scan just can't match.
Still have questions? Our experts are here to help. For a no-obligation chat about your specific security concerns and how F1Group can help, Phone 0845 855 0000 today or Send us a message.