Endpoint protection is all about putting a digital bodyguard on every single device that connects to your business network. It's a non-stop, active defence system designed to keep your company data safe, whether it's on a laptop, a server, or a mobile phone. This has become absolutely essential as cyber threats, particularly ransomware, continue to hit businesses hard.
What Are Endpoints and Why Do They Need Protection?
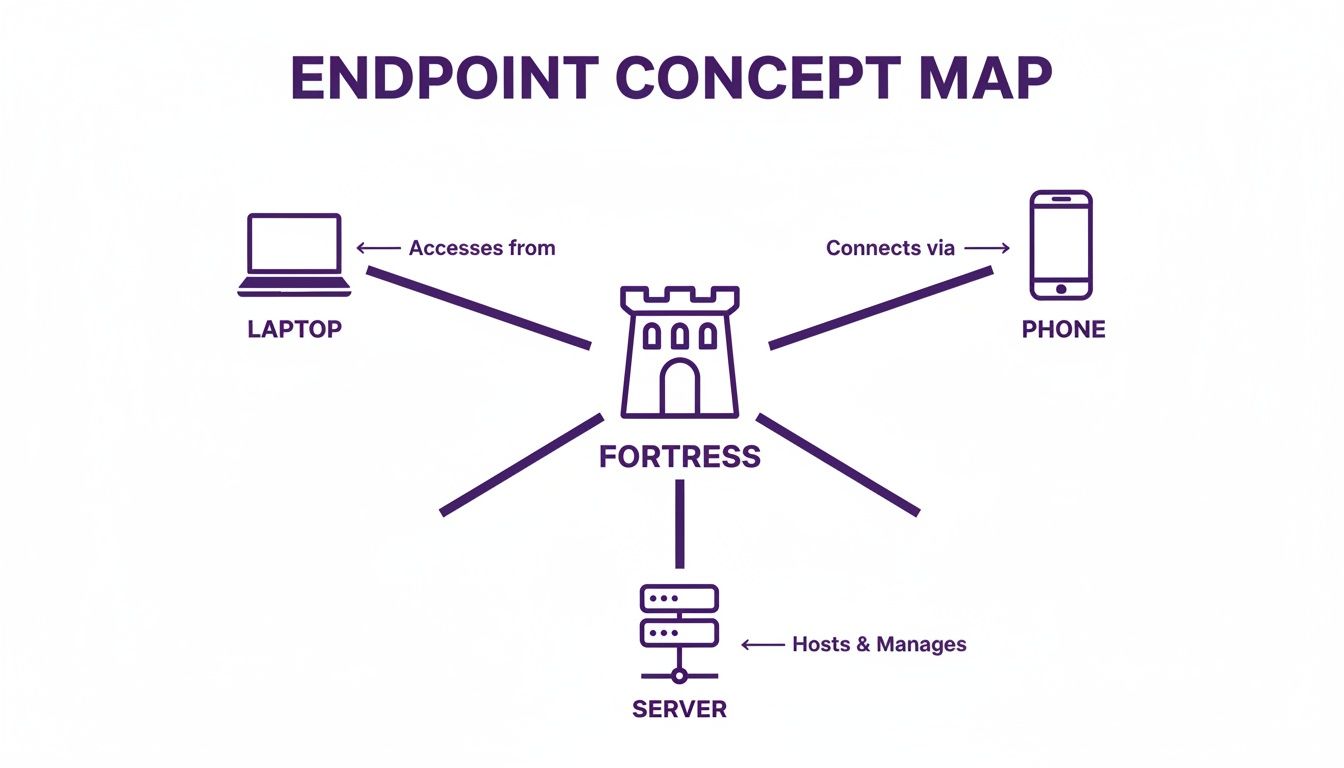
Think of your business like a castle. A few years ago, that castle had one big, heavily guarded gate – your office network. Everyone worked inside the walls, so you just needed to focus your security on that single perimeter. Simple enough.
Fast forward to today, and that castle now has hundreds of doors and windows flung wide open. Each laptop, mobile phone, server, and even smart device your team uses for work is an endpoint. And every single one is a potential way in for a cybercriminal.
This is the new front line of your company's security. With hybrid working and cloud services like Microsoft 365 and Azure now standard, your data no longer lives neatly inside the old office network. Your people and your critical information are spread out everywhere.
The old security model of just guarding the main gate simply doesn't cut it anymore. You need digital sentries watching every one of those doors and windows, 24/7. That's exactly what endpoint protection services are for.
The Modern Threat to UK Businesses
This isn't just a hypothetical problem; it's a very real and present danger for businesses across the UK. Cyber attacks are becoming more common and far more clever, targeting the very devices your team relies on every day.
The UK endpoint security market, currently valued at around £580 million in 2024, is expected to grow by 8.3% annually. This isn't just industry spending; it's a direct response from businesses scrambling to put stronger defences in place. Find out more about the UK endpoint security market
The National Cyber Security Centre (NCSC) paints a sobering picture. A recent report revealed that ransomware attacks on UK organisations jumped by a massive 64% in just one year. As a result, British companies are now spending an estimated £1.9 billion every year on endpoint security just to stay safe.
Why Every Device Matters
It only takes one unprotected device to bring your entire business to its knees. An employee working from a coffee shop clicks a dodgy link on their laptop, or a work phone gets infected, and suddenly an attacker has a way in.
From that one weak point, they can:
- Steal sensitive client information or your company's trade secrets.
- Launch a ransomware attack, locking up your files and grinding your business to a halt.
- Worm their way into your main network and other critical systems.
Proper endpoint protection acts as a crucial security layer that travels with your employees and your data, wherever they go. It makes sure that every device—every potential entry point into your castle—is constantly watched, managed, and defended against the threats we face today.
The Core Technologies Inside Modern Endpoint Protection
To really get to grips with modern endpoint protection, you need to lift the bonnet and look at the powerful technologies working together. It’s not just one piece of software; it’s a whole team of components forming a multi-layered defence. Each part has a specific job in spotting, blocking, and responding to cyber threats, securing every possible way into your business.
Think of it like this: every laptop, phone, and server is a potential doorway into your company's central fortress.
When you see your network this way, it becomes obvious why a single firewall isn't enough. Your security has to reach every single connected device.
To understand how this all fits together, let’s break down the main technologies you'll find in a good endpoint protection service. Traditional antivirus is the old guard, but it's now supported by newer, more intelligent systems like EDR and XDR.
This table gives a quick overview of how they compare.
Key Endpoint Protection Technologies Explained
| Technology | Primary Function | Analogy | Best For |
|---|---|---|---|
| Traditional Antivirus (AV) | Blocks known threats using a signature database. | A bouncer with a list of known troublemakers. | Stopping common, well-documented malware. |
| Endpoint Detection & Response (EDR) | Monitors for suspicious behaviour on devices. | CCTV and an on-site security team watching for odd activity. | Catching new, sophisticated threats that AV might miss. |
| Extended Detection & Response (XDR) | Connects security data from all sources (endpoints, cloud, email). | An intelligence network linking all security teams together. | Getting the full picture of a complex, multi-stage attack. |
Each technology builds on the last, creating a much stronger and more comprehensive defence than any single tool could offer alone. Now, let's dive into what each one actually does.
Antivirus: The Foundational Gatekeeper
Most people are familiar with traditional antivirus (AV). It’s been the bedrock of cyber security for decades. It works by scanning files and comparing their digital 'fingerprints' against a huge, constantly updated list of known malware.
If it finds a match, it blocks the file. Simple and effective. AV is still brilliant at stopping a massive volume of common threats before they can do any damage.
But its reliance on that list of known threats is also its Achilles' heel. Cybercriminals are always cooking up new malware that hasn't been seen before, and this new stuff can often waltz straight past traditional AV. That’s where the next layers come in.
Endpoint Detection And Response: The On-Site Security Team
If antivirus is the bouncer, Endpoint Detection and Response (EDR) is the high-tech CCTV system combined with an on-site security team patrolling the grounds. It doesn’t just look for known criminals; it actively monitors for suspicious behaviour.
EDR solutions constantly gather data from all your endpoints – laptops, servers, you name it. They watch for patterns that might signal an attack, even if the malware itself is brand new.
For example, EDR would raise a red flag if a Microsoft Word document suddenly tried to encrypt all your files or connect to a server in a different country. It gives security analysts the tools to investigate, instantly isolate the device to stop the threat from spreading, and figure out exactly how the breach happened. This proactive approach is what you need to catch the clever attacks that get past basic AV.
Extended Detection And Response: The Intelligence Network
Extended Detection and Response (XDR) takes the idea behind EDR and dials it up to eleven. It expands that watchful eye across your entire IT environment. It’s not just watching your endpoints; it connects the dots between your laptops, cloud apps, email systems, and network firewalls.
XDR is all about creating a single, unified view of your security. It pieces together alerts from different systems to paint a complete picture of an attack, leading to much faster and more accurate responses.
Imagine this: a hacker sends a phishing email (spotted by your email gateway). An employee clicks a link and downloads malware to their laptop (spotted by EDR). That malware then tries to steal data from your cloud storage (spotted by your cloud security). An XDR platform pulls all those separate alerts together into one single, cohesive incident, showing you the full story of the attack.
Other Essential Components
Beyond those core three, a proper endpoint protection service packs in several other vital functions:
-
Vulnerability Scanning and Patching: This process automatically finds missing security updates and weaknesses on your devices. It then applies the right patches to close those security holes before attackers can get through them.
-
Device Control: This lets you control what can be plugged into your company devices, like USB sticks or external hard drives. By blocking unauthorised gadgets, you can stop malware from being physically introduced to your network. For more on this, check out our guide on mobile device management with Intune.
-
Encryption: Full-disk encryption makes sure that if a laptop or phone is lost or stolen, the data on it is completely unreadable. It essentially scrambles the information, making it worthless to anyone who doesn’t have the key.
Managed Services vs. In-House Security: A Practical Comparison
Deciding how to handle your endpoint security is one of the most important calls a business leader will make. Do you build your own internal team, or do you bring in a specialist provider of endpoint protection services? This isn't just a software choice; it's a decision that impacts your strategy, budget, and overall resilience.
Let's break down the real-world pros and cons of each path. My goal is to give you a balanced view so you can make the right call for your company's security and its future.
The In-House Security Approach
On the surface, having an in-house security team sounds ideal. You get direct control, with dedicated staff who live and breathe your business, its unique risks, and its internal culture. It can feel like the safest bet.
However, the reality of building and sustaining a truly effective security operation is riddled with challenges that are very easy to underestimate.
Key Challenges of In-House Security:
- High and Unpredictable Costs: This is often the biggest shock. A single, experienced cybersecurity analyst in the UK can command a salary of over £60,000 per year, and you'll almost certainly need more than one to provide proper cover. On top of that, you have to budget for their constant training, certifications, and the sophisticated (and expensive) tools they need to do their jobs.
- The 24/7 Monitoring Burden: Cyber threats don’t work 9-to-5. A breach can just as easily happen at 3 AM on a bank holiday weekend. To provide genuine round-the-clock protection, you need a multi-person team working in shifts, which is simply out of reach for most small and mid-sized organisations.
- The Constant Race Against Threats: The threat landscape changes by the hour. Your team has to stay on top of the latest attack vectors, software vulnerabilities, and defence tactics. This continuous learning curve is a full-time job in itself and can quickly swamp a small IT department that's already juggling other responsibilities.
The Managed Services Advantage
Partnering with a Managed Security Service Provider (MSSP) offers a completely different way forward. Instead of building from the ground up, you get immediate access to a seasoned, fully-equipped team of security experts. It's a model that is quickly becoming the default for smart UK businesses.
In fact, the UK is seeing a major shift towards managed services, which are set to command a 62.73% market share by 2025. This move is driven by the reality that in-house expertise is hard to find and even harder to retain. It's a trend we see right here in the East Midlands, as businesses embracing tools like Microsoft 365 realise they need a partner to secure everything properly.
For many, the first step is understanding what managed cybersecurity services actually involve. It’s not just about outsourcing a task; it's about forming a strategic partnership.
Strategic Benefits of Managed Services:
- Immediate Access to Expertise: From day one, you have a team of certified, DBS-checked security specialists on your side. They bring a wealth of experience gained from defending hundreds of different businesses—a level of insight an in-house team might take years to develop.
- Predictable and Simplified Budgeting: Instead of facing chunky, unpredictable capital costs, you pay a fixed monthly fee. This operational expense model makes budgeting for first-class security straightforward and predictable, often coming in at a fraction of the cost of just one security analyst's salary.
- Freeing Up Your Internal Team: By offloading the daily security grind, you empower your own IT staff. They can stop putting out fires and reacting to endless alerts, and instead focus on the strategic projects that actually grow your business.
By partnering with a provider for your endpoint protection services, you are not just buying a tool; you are investing in a security outcome. It's the difference between buying gym equipment and hiring an expert personal trainer who guarantees you'll get results.
Ultimately, the right choice boils down to your organisation's size, resources, and tolerance for risk. But for a growing number of UK businesses, the expertise, cost-efficiency, and strategic focus offered by managed IT security services presents a clear and powerful advantage.
Calculating the Real Business Value and ROI
Thinking about endpoint protection services purely as an IT expense is missing the point. It’s not just another piece of software; it’s a strategic business decision with a very real, very measurable return on investment (ROI). To get the full picture, you have to look beyond the technical jargon and focus on what it actually delivers: business continuity, brand integrity, and long-term resilience.
The clearest way to see the ROI is to weigh the predictable, manageable cost of protection against the chaotic, potentially crippling cost of a security breach. It’s simply proactive spending versus reactive panic.
The Cost of Doing Nothing
A single successful ransomware attack can have a devastating financial impact, and the damage goes far deeper than just the ransom demand. For a mid-sized organisation, the true cost is a cocktail of expenses that can easily spiral into six figures.
The financial fallout from a breach often includes:
- Remediation and Recovery: This covers everything from hiring forensic experts to figure out what happened, to rebuilding your systems from the ground up and restoring data.
- Lost Revenue: Every minute your systems are offline is a minute you aren't serving customers, taking orders, or making money. The clock is ticking.
- Regulatory Fines: If customer data is compromised, you could be facing hefty fines for non-compliance with regulations like GDPR.
- Reputational Damage: This is the big one. Losing the trust of your customers can be the most damaging cost of all, hitting future sales and poisoning business relationships for years to come.
This isn't a distant threat; it's happening right here, right now. UK organisations, for instance, saw a staggering 40% increase in cyberattacks targeting banks in 2022. It's no surprise that the financial services sector now makes up 25.9% of Europe's entire endpoint security market. With ransomware attacks jumping 64% in that same period, the £1.9 billion that UK businesses now spend annually on security is a direct, necessary response. You can explore more on these trends in the European endpoint security market report.
The Proactive Investment Model
Now, let's contrast that nightmare scenario with the cost of a managed endpoint protection service. For a predictable monthly fee—often somewhere between £10 to £20 per endpoint—you get access to top-tier security technology and, crucially, a team of experts whose entire job is to stop these incidents from ever happening.
This predictable operational expense effectively transforms a potentially business-ending financial disaster into a manageable, budgeted line item. It’s the difference between paying for a robust security alarm system and paying to rebuild your house after a fire.
Quantifying the Tangible Returns
The ROI becomes crystal clear when you start tallying up the benefits that go beyond just preventing a breach.
- Reduced Downtime: By stopping malware and ransomware in their tracks, these services prevent the kind of operational paralysis that brings a business to a screeching halt. This directly protects your revenue and keeps your team productive.
- Protected Brand Reputation: Preventing a public data breach is priceless. It safeguards the trust you’ve worked so hard to build with your customers, suppliers, and partners.
- Simplified Compliance: Modern endpoint protection is a huge help in achieving and maintaining compliance with data protection laws. It provides essential controls like data encryption and access monitoring that regulators want to see.
When you put it all together, the business case is compelling. A modest, predictable monthly investment completely neutralises the risk of a six-figure catastrophe, all while making your operations smoother and protecting your company’s most valuable asset—its reputation.
Give us a call on 0845 855 0000 today to discuss how we can help protect your business. You can also send us a message to arrange a consultation.
How to Choose the Right Endpoint Protection Partner
Picking a partner to handle your company's security is one of the most important decisions you'll make. It’s not about ticking a box or buying a piece of software; you're placing a huge chunk of your operational resilience in someone else's hands. To get it right, you need to look past the glossy brochures and start asking some tough questions.
This isn’t just about finding a supplier. It's about finding a partner that feels like a genuine extension of your own team. This practical checklist will help you cut through the noise and find a provider who not only has the technical chops but actually understands your business goals.
Evaluate Their Technical Expertise and Focus
First things first, you need to be sure they have deep, proven expertise in the tech your business actually uses day-to-day. A one-size-fits-all approach to security just doesn't cut it anymore. You need specialists.
For many businesses here in the East Midlands, that means a laser focus on the Microsoft ecosystem. Does the provider have certified experts in Microsoft 365 and Azure? Their ability to properly secure these platforms is absolutely non-negotiable, since that's where most of your sensitive data lives and where your people get their work done.
A great partner doesn’t just sell you a tool. They should demonstrate how their endpoint protection services integrate perfectly with your existing IT infrastructure to create a seamless, unified defence.
You also need to see proof of their qualifications. Don’t be afraid to ask about their team's certifications. Crucially, are their engineers DBS-checked? This gives you peace of mind that the people with privileged access to your systems are trustworthy and have been properly vetted—a vital step in any security relationship.
Look for Proactive Defence, Not Just Reactive Alerts
Here’s one of the biggest things that separates an average provider from an excellent one: their mindset. Far too many providers will simply forward a flood of automated security alerts to your inbox, leaving you to figure out what’s a real threat and what’s just noise. That’s not a partnership; it’s a distraction.
A top-tier partner, on the other hand, offers proactive threat hunting. This means their security team is actively searching for signs of compromise across your network, looking for the subtle clues and anomalies that automated systems often miss. Think of them as digital detectives constantly patrolling your environment.
When vetting potential partners, really dig into how they handle incidents:
- Incident Response: When a threat is detected, what happens next? Do you take full ownership of investigating, containing, and resolving the issue?
- Communication: How will you keep us in the loop during a security event? Who is our dedicated point of contact?
- Reporting: What kind of reports will we get? We need to see what you're doing and understand the value you’re providing.
Ensure the Solution Can Scale With Your Business
Your business isn't going to stand still, so your security partner can't either. The right provider will offer a service that grows and adapts right alongside you. Whether you're hiring ten new employees or expanding into a new market, your security coverage needs to scale effortlessly without forcing you into a massive, disruptive overhaul.
Talk to them about their onboarding process for new devices and users. Ask how they handle changes in your business structure. A flexible, scalable service is the only way to ensure your protection remains watertight, no matter how your organisation evolves. By focusing on these key areas—expertise, proactivity, and scalability—you can confidently choose a partner who will truly safeguard your business.
Ready to take the first step towards better security? Phone us on 0845 855 0000 today or Send us a message to chat with our team about your needs.
Securing Your Business From Every Angle
In the modern business environment, solid cybersecurity isn't just an IT issue anymore—it's become a cornerstone of your entire operation. Every single laptop, phone, and server is a potential way in for an attacker, which is why a professionally managed, proactive approach to endpoint protection is your most reliable defence.
Throughout this guide, we’ve seen how these services go far beyond traditional antivirus. They use sophisticated tools like EDR to actively hunt for threats and shut down attacks before they can cause real financial damage. The real value here isn't just about dodging a bullet; it's about creating a secure foundation for confident growth.
When your devices are safe, you're also protecting your reputation, keeping the business running smoothly, and maintaining the trust you've built with your clients. This frees up your team to concentrate on what they do best: moving the business forward.
Think of a managed security partner not as an expense, but as an investment in business continuity and genuine peace of mind. It’s about having experts in your corner, making sure every angle is covered.
A truly comprehensive security strategy also means locking down your collaboration tools. For businesses running on Microsoft 365, it’s worth looking into expert SharePoint migration services to ensure your data is both secure and properly organised from the start. To dig deeper into shoring up your defences, have a read of our guide on how to prevent ransomware attacks.
It's time to take that decisive step to safeguard your business's future.
Give us a call on 0845 855 0000 today, or Send us a message.
Got Questions About Endpoint Protection? We've Got Answers.
Stepping into the world of cybersecurity can feel like learning a new language. As a business leader, you just need clear, straight answers to make smart decisions about protecting your company. We've gathered the most common questions we hear about endpoint protection to cut through the noise.
Let's clear up the jargon and give you the practical insights you need.
What’s The Real Difference Between Antivirus And Endpoint Protection?
It’s a common point of confusion, but they’re worlds apart.
Think of a traditional antivirus as a bouncer at a nightclub with a list of known troublemakers. If someone on the list tries to get in, they're stopped. It's effective against common, known viruses, but that's where its job ends.
Endpoint protection is the entire security team for the venue. It includes the bouncer (antivirus), but also adds CCTV cameras, roaming patrols, and access control. This is your Endpoint Detection and Response (EDR), which actively hunts for suspicious behaviour, not just faces on a list. It also enforces rules, like who can use certain doors (USB device control), creating a complete, layered defence system.
How Much Do Endpoint Protection Services Typically Cost In The UK?
There's no single price tag, but for a managed service in the UK, you're generally looking at a range of £5 to £25 per user, per month.
What pushes the price to the lower or higher end of that scale? A few things:
- Number of Devices: How many laptops, servers, and mobiles need protecting?
- Level of Tech: Are you after a solid baseline platform, or do you need advanced EDR and XDR capabilities for a higher-risk environment?
- Management Scope: How much hands-on support, monitoring, and incident response is included in the service?
It's helpful to see this as a predictable operational expense, not a cost. When you contrast a manageable monthly fee with the potentially crippling six-figure sum needed to clean up after a single cyberattack, it becomes a strategic investment in business continuity.
We’re A Small Business. Do We Genuinely Need This Level Of Protection?
Yes, absolutely. In fact, you're precisely who the cybercriminals are targeting now. Attackers know that small and medium-sized businesses often have stretched resources and assume they have weaker security, making them a softer target than a huge corporation.
For an SMB, a single ransomware attack or data breach isn't just an inconvenience; it can be a company-ending event. The combination of financial loss, regulatory fines, and reputational damage is often too much to recover from. Advanced endpoint protection levels the playing field, giving you enterprise-grade security that’s affordable and manageable for a growing business.
Can Endpoint Protection Stop Every Single Cyberattack?
It's important to be realistic: no security tool on earth can promise to stop 100% of threats. Cybercriminals are constantly inventing new ways to attack, and it's a non-stop cat-and-mouse game.
However, a modern endpoint protection platform massively reduces your chances of being successfully breached. Its first job is to automatically block the overwhelming majority of threats dead in their tracks. For the rare, sophisticated attack that might slip through, the platform’s real value shines. It provides the tools to instantly detect, investigate, and shut down the threat before it can spread and cause real damage. It’s this rapid response that turns a potential disaster into a minor, contained incident.
Ready to secure your business with expert, locally-focused F1Group endpoint protection services?
Phone 0845 855 0000 today or Send us a message to discuss your security needs with our team.
Phone 0845 855 0000 today or Send us a message https://www.f1group.com/contact/