Let's be blunt: your general IT support team, as good as they are, are not cyber security experts. Thinking they are is like asking your family GP to perform open-heart surgery. The skills are related, but the specialism—and the stakes—are worlds apart.
What IT Security Experts Do and Why You Need Them
An IT security expert’s job is singular: protect your company’s systems, networks, and data from attack. They aren’t there to fix printer jams or software glitches. They are your digital sentinels, designing defences, hunting for weaknesses, and responding with force when an attack happens.
As your business grows and embraces powerful tools like Microsoft 365 and Azure, your digital footprint expands. Every new cloud service, every new user account, is another potential door for an attacker. These aren't just hypothetical risks; they are active threats happening right now.
Don’t just take our word for it. A recent government report found that nearly one-third of UK businesses (32%) and over a fifth of charities (22%) suffered a cyber security breach or attack in the last 12 months. The threat is real, and it is constant.
Closing the Critical Skills Gap
Finding, hiring, and retaining genuine security talent is a massive challenge. There's a well-documented skills gap across the UK, and it's felt keenly by organisations here in the East Midlands. From growing firms in Lincoln to established names in Nottingham, many simply can't find or afford the in-house team they need.
This is where turning to external IT security experts makes so much sense. Their entire world revolves around:
- Designing Secure Systems: They build your networks and cloud environments securely from day one, not as an afterthought.
- Proactive Threat Hunting: They don't wait for alarms. They actively search your systems for vulnerabilities before criminals find them.
- Incident Response: When an attack does occur, they are the ones who contain the breach, neutralise the threat, and get you back to business with minimal damage.
- Ensuring Compliance: They help you navigate the legal minefield of regulations like GDPR, ensuring your data practices are compliant.
Working with specialists gives you immediate access to a depth of expertise that would take years to build internally. It’s the most direct way to protect your operations, your reputation, and your bottom line.
Ready to secure your business? Phone 0845 855 0000 today or Send us a message to speak with an expert.
The UK's Cyber Security Skills Shortage: What It Means for Your Business
If you've tried hiring a cyber security specialist in the UK recently, you know the struggle is real. It can feel like you’re chasing a ghost. The pool of qualified, experienced candidates seems to shrink by the day, while the competition for them becomes more and more intense.
This isn't just a feeling; it’s a well-documented skills shortage. While the number of people entering the security profession is growing, demand from businesses is growing even faster. This imbalance inevitably drives up recruitment times, salary demands, and the sheer cost of getting the right person on board.
The East Midlands Reality: A Local Fight for Talent
For any small or medium-sized business in the East Midlands, this national crisis hits particularly close to home. If you’re an IT Director in Leicester or a business owner in Scunthorpe, you're not just competing with other local firms. You're up against the huge budgets and undeniable draw of major corporations in London and other big cities.
Let's be honest, the most seasoned security experts are often lured away by these larger enterprises, creating a talent vacuum right here in our region. This leaves local businesses in a tough spot—exposed and under-protected, not because they don't care about security, but because the very experts they need are simply out of reach.
The UK's cyber security workforce is expected to grow to between 143,000 and 150,000 by 2026. Despite this 5% year-on-year increase, a stubborn gap of 25,000 unfilled roles is predicted to remain. This shortfall has an outsized impact on SMEs in regions like the East Midlands, where the demand for experienced professionals is high but the local talent pool is thin. You can dig into the numbers yourself with the UK's cyber security workforce gap statistics on StateGlobe.com.
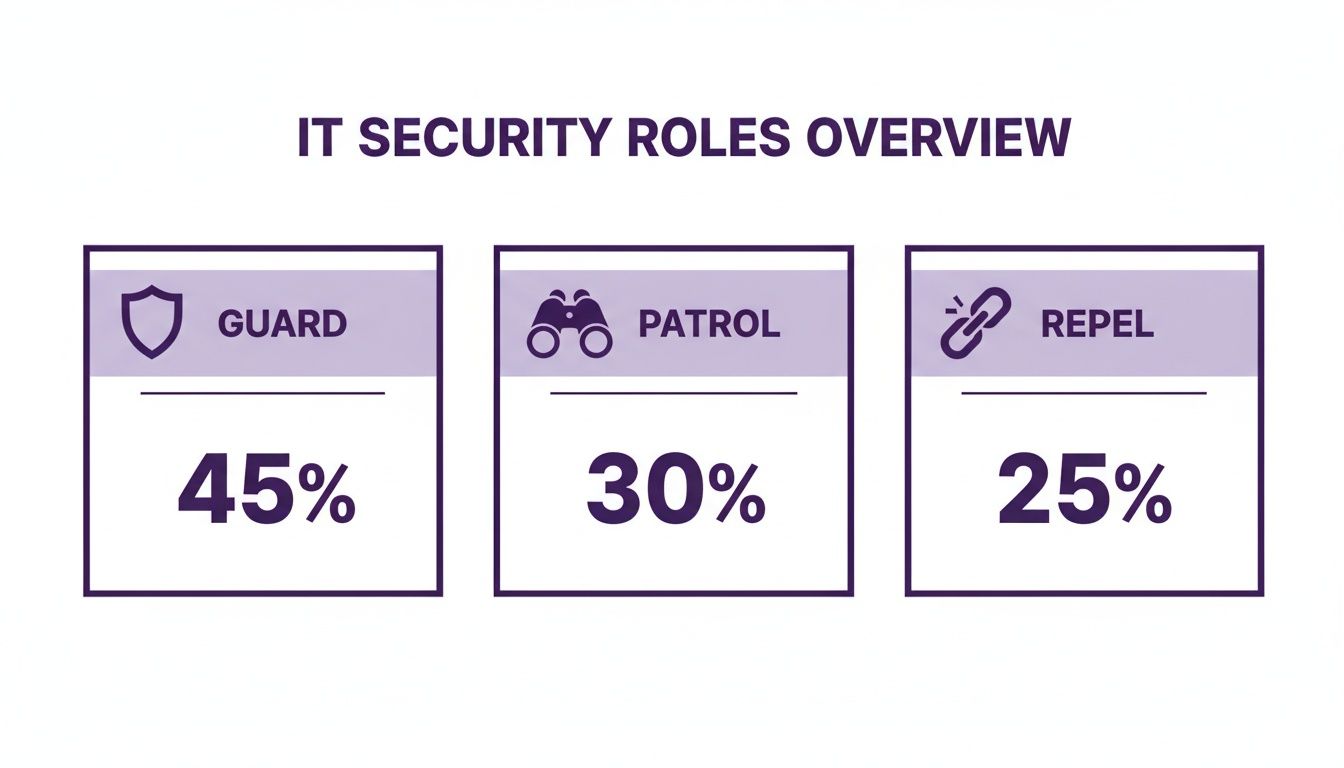
The data shows that nearly half of all UK businesses admit they lack the in-house skills to handle their security. It’s no wonder, when you consider all the roles a single expert is expected to fill—guarding the perimeter, patrolling for emerging threats, and actively repelling attacks.
When one person is stretched this thin, something has to give. This forces business leaders like you to rethink the entire approach to getting the right expertise.
A More Practical Way to Bridge the Gap
Instead of continuing the frustrating search for a single person who might not even be in the local market, there's a much more effective strategy. Working with a managed security service provider gives you immediate access to an entire team of IT security specialists, without the cost and hassle of recruitment.
It’s a straightforward, powerful way to get the enterprise-grade protection you need. You get the benefit of a deep bench of talent that’s focused on your specific challenges, freeing you up to focus on what you do best: running your business.
Ready to close your security gap for good? Give us a call on 0845 855 0000 or Send us a message to see how we can help.
Decoding the Skills of an Elite Security Expert
When you bring in an IT security partner, what are you actually paying for? It’s a fair question. After all, not all IT support is the same, and the difference between a generalist and a true security specialist is massive.
A genuine expert brings a specific blend of deep technical knowledge, forward-thinking strategy, and hard-won experience. Knowing what to look for helps you understand the value you're getting and ensures you're not just paying for a fancy title.
Instead of getting bogged down in a sea of technical jargon, it’s easier to think about these skills in terms of the practical roles they fill. A complete security posture isn't about one person doing everything; it's about a team of specialists working together. An external provider should give you access to all of them.
The Core Roles of a Security Team
Here are the key players you need on your side:
-
The Architect: This is your master planner. The Architect designs your network and cloud systems to be secure from the very beginning. They ensure platforms like Microsoft Azure are configured for robust security, not just for basic functionality. Their work is all about prevention, stopping vulnerabilities before they even have a chance to appear.
-
The Guardian: Think of the Guardian as the guard on the night watch, keeping a constant eye on your digital borders. They manage your firewalls, actively monitor network traffic for anything unusual, and hunt for threats 24/7. This is your real-time, frontline defence against active attacks.
-
The Investigator: When an alarm goes off, the Investigator steps in. With a background in digital forensics and incident response, their job is to figure out what happened. They meticulously trace the steps of an attack to understand the how, what, and when of a breach, before kicking the intruder out and securing the system for good.
Certifications are more than just letters after a name. They are the industry's way of verifying that an individual has proven, tested expertise in these critical roles. This validated knowledge is what keeps your business safe.
Key Certifications and What They Really Mean
Top-tier security professionals back up their experience with demanding industry certifications. Someone holding a CISSP (Certified Information Systems Security Professional), for instance, has proven their ability to think strategically about security across an entire organisation. A CISM (Certified Information Security Manager) demonstrates expert-level skill in governing and managing a company's information security programme.
Today, with so much business happening in the cloud, Microsoft-specific credentials are non-negotiable. Certifications like SC-200 (Microsoft Security Operations Analyst) and AZ-500 (Microsoft Azure Security Technologies) are proof that an expert has hands-on, validated skills to protect your Microsoft 365 and Azure environments specifically. The tech world is increasingly focused on this kind of demonstrated ability, which is why we're seeing a major shift toward valuing skills over degrees in tech hiring.
Essential Services That Protect Your Business
Bringing in external IT security experts isn’t about getting a vague promise of "protection." It’s about putting specific, powerful services in place to guard against the very real threats businesses face today. Each service acts as a specialised tool, working together to build a truly resilient defence for your company.
Think of it like securing a physical building. You wouldn't just rely on a single lock on the front door, would you? Of course not. You'd have alarms, CCTV, and someone keeping an eye on things. Professional IT security services provide this exact kind of layered defence, but for your digital world.
Managed Security Operations Centre (SOC)
A Managed SOC is your 24/7 digital watchtower. It’s a dedicated team, backed by serious technology, that constantly monitors your entire IT environment—from your network and servers to your cloud platforms—for any sign of trouble. This is the crucial difference between finding out you’ve been breached months after the damage is done, and stopping an attack dead in its tracks.
A great SOC service doesn’t just sound an alarm and walk away. They investigate the threat, confirm if it’s real, and then act on it immediately. For most small and medium-sized businesses, building and staffing this kind of round-the-clock operation in-house is simply out of reach, which makes a managed service both a powerful and a practical choice.
Proactive Vulnerability Management
Think of Vulnerability Management as giving your digital infrastructure a regular, thorough MOT. Instead of waiting for something to go wrong (or for a hacker to break in), this service systematically scans your systems to find the weak spots first. It hunts for outdated software, sloppy configurations, and other security gaps that criminals love to exploit.
A proactive approach is absolutely essential. Attackers use automated tools that are constantly scanning the internet for these known vulnerabilities. Finding one is like them discovering you’ve left the back door wide open. Regular vulnerability management keeps those doors locked.
An expert won’t just hand you a long list of problems. They’ll prioritise the weaknesses based on how risky they are, giving you a clear, actionable plan to get the most critical issues fixed first. To get a better sense of where you stand right now, our cyber security audit checklist is a great place to start.
Securing Your Microsoft Ecosystem
With so many businesses running on Microsoft 365 and Azure, making sure these platforms are locked down is no longer optional. IT security experts offer specialised services designed to harden these environments against attack. This goes far beyond just setting up user accounts and passwords. It means:
- Securing Microsoft 365: Putting advanced threat protection in place for your email, setting up policies to prevent sensitive data from being accidentally leaked, and properly managing who has access to what within your files and Teams chats.
- Protecting Azure Infrastructure: Making sure your cloud servers and applications are correctly configured from the ground up, with the right network controls and monitoring to spot any unauthorised activity in your cloud environment.
- Safeguarding AI and Copilot: With new tools like Microsoft Copilot changing how we work, experts help you build the right security rules. This ensures your team can use these amazing AI tools without putting sensitive company information at risk.
To give you a clearer picture, here’s a quick breakdown of how these services directly benefit your organisation.
Essential IT Security Services for Your Business
| Service | What It Does | Primary Business Benefit |
|---|---|---|
| Managed SOC | Provides 24/7 monitoring, detection, and response to cyber threats across your entire IT estate. | Prevents breaches by stopping attacks in real-time, minimising disruption and financial loss. |
| Vulnerability Management | Proactively scans for and prioritises security weaknesses like unpatched software and misconfigurations. | Reduces your attack surface by systematically closing security holes before hackers can find them. |
| Microsoft 365/Azure Security | Hardens your cloud platforms with advanced threat protection, identity management, and secure configurations. | Protects critical data where your team works every day, ensuring compliance and secure collaboration. |
| Copilot/AI Security | Establishes governance and data protection policies for the use of AI tools within your business. | Enables safe innovation by allowing your team to use powerful AI without risking data exposure. |
Ultimately, focusing on these specific areas delivers tangible results for your business. It's about reducing financial risk, staying compliant with regulations, and building a stronger, more resilient organisation for the long haul.
How to Hire IT Security Experts: A Practical Checklist
Finding the right IT security experts can feel like navigating a minefield, but it doesn't have to. With a clear, structured approach, you can cut through the noise and find a partner who truly gets your business, not just the technology. This checklist walks you through the essential steps, from initial planning to making that final, confident choice.
Think of it as a roadmap. Following it ensures you cover all your bases and land on an expert team that’s a perfect fit for what you need to achieve.
Define Your Security Perimeter
Before you even think about talking to potential partners, you need to look inward. The first and most critical question is simple: what are you actually trying to protect? Your "security perimeter" isn't the four walls of your office; it’s everywhere your data lives, moves, and is used.
Start by making a frank list of your most valuable digital assets. This might include:
- Customer databases and sensitive financial records.
- Intellectual property, like unique designs, formulae, or strategic plans.
- Operational systems that keep your business running day-to-day.
- Employee data and other personal information you're responsible for.
Once you know what matters most, you can have a much more productive conversation. A good partner can then explain how they’ll protect those specific assets, moving beyond generic sales pitches.
Vet Potential Partners Thoroughly
Now that you know what you need, it's time to find the right people to deliver it. Vetting is all about digging for proof of expertise and reliability. Don’t just take a company's marketing at face value; you need to see real evidence.
Look for industry-recognised certifications that are relevant to your business, especially if you rely on Microsoft tools—think SC-200 or AZ-500. Ask them for case studies or, even better, to speak with a reference from a business similar to yours, particularly one in the East Midlands. This gives you a true feel for their performance and how they treat their clients. While you can streamline some of these checks with tools like the Hire-Sense platform, a direct conversation is invaluable.
A strong track record is your best indicator of future success. Look for a partner with proven experience in your sector and a history of long-term client relationships. This demonstrates they deliver consistent value over time.
Choose the Right Engagement Model
How you’ll work together is just as important as who you work with. The structure of the relationship needs to fit your requirements. Typically, you'll encounter two main models:
- Retainer-Based: This is perfect for ongoing protection, like a Managed SOC or continuous vulnerability management. You pay a predictable monthly fee for constant vigilance and access to a team of experts whenever you need them.
- Project-Based: This is better suited for one-off tasks. Think of a specific security audit, a penetration test, or a project to harden a new system. You pay a fixed fee for a clearly defined piece of work.
Ask Crucial Questions
When you get down to final discussions, don't hold back. This is your chance to ask the tough, specific questions that reveal true expertise. Ask them to walk you through their incident response process—what exactly happens, step-by-step, when they detect an attack?
If Microsoft 365 and Azure are the heart of your operations, probe their expertise there. A genuinely skilled partner will have clear, confident, and detailed answers. To help you structure these important questions, you might find our RFP IT template useful.
By taking these steps, you can move forward with the assurance that you’ve chosen the right IT security experts to protect your business.
Ready to find your expert security partner? Phone 0845 855 0000 today or Send us a message.
What Does Expert Security Actually Cost? (And Is It Worth It?)
Let's talk about the numbers. Bringing in IT security experts is a serious decision, and it’s easy to focus on the initial cost. But it’s far more helpful to see it as an investment in your company’s future, not just another expense on the balance sheet. In the UK, how you pay for that expertise usually falls into one of a few common models, each designed for different business needs.
The structure of your engagement really depends on what you're trying to achieve. For continuous, round-the-clock protection like a Managed Security Operations Centre (SOC), a monthly retainer is the standard. This gives you predictable costs and constant vigilance. For a small or medium-sized business, this could be anywhere from £1,500 to over £5,000 per month, depending on the size and complexity of your digital footprint.
On the other hand, you might have a specific, one-off goal. Maybe you need a penetration test to proactively find weak spots or a full security audit before launching a new platform. For these kinds of defined projects, a fixed, project-based fee makes the most sense. And for quick advice or emergency support, most experts will work on a simple hourly or daily consultancy rate.
The Real Return on Your Investment
It’s tempting to get sticker shock from a monthly fee, but the real value becomes crystal clear when you weigh it against the devastating cost of a security breach. Put simply, effective security run by specialists dramatically lowers your risk. We’ve seen that hands-on support from a dedicated partner can slash security risks by over 50% for many organisations.
The reality is that 43% of UK SMEs simply can't afford dedicated, in-house security teams. Even for those that can, a persistent skills gap of 25,000 roles means finding the right people is a huge challenge. This data, highlighted in reports from sources like Firebrand Training, shows why partnering with an external expert is often the smartest business decision.
But the ROI isn’t just about dodging a financial bullet. It’s about building a resilient business that can operate with confidence. It’s about meeting your GDPR obligations, protecting your hard-earned reputation, and giving you the peace of mind that your most valuable assets are properly defended.
When you look at the full picture, the value of our IT managed security services becomes undeniable.
Ready to discuss a security investment that makes sense for your business?
Phone 0845 855 0000 today or Send us a message.
What's Your Next Step Towards a More Secure Business?
If there’s one thing to take away from this guide, it’s that proper IT security is no longer a luxury reserved for the giants of industry. It's now a fundamental part of doing business for everyone. The simple truth is that today's threats require more than just standard IT support; they demand specialists who live and breathe defence.
We've walked through the real-world difficulties of hiring this talent in-house, especially with the UK's well-documented cyber security skills gap. We also laid out the key services you should be looking for and gave you a practical checklist to use when you're ready to bring in external security experts.
For businesses across the East Midlands, from Lincoln to Leicester, working with an experienced local provider is the most direct route to getting enterprise-grade security. It gives you that deep bench of talent on day one, without the eye-watering costs and headaches of recruitment.
Procrastination is a cybercriminal's greatest ally. Every day you put off strengthening your defences is another day you're leaving the door wide open. The time to move from knowing to doing is right now.
At the end of the day, this is about so much more than protecting data. It’s about protecting your reputation, your operations, and your future. It's about building a resilient business that can operate with confidence, no matter what comes next.
It's time to take that decisive step and protect what you've worked so hard to build.
Speak with one of our F1 Group specialists to discuss how we can secure your business.
Phone 0845 855 0000 today or Send us a message to schedule your consultation.